Outdated software and vendor lock
Outdated software and vendor lock-in
Vendor lock-in is one of the most expensive problems of modern business and at the same time one of the most underrated. The system works, but development is slow, vendor prices are rising, changes take months, and switching to another solution seems impossible. This is not a technical problem. It's about misconfigured cooperation terms and outdated architecture that ties your hands. We specialize in exactly these situations: we take over your software, perform a thorough dependency analysis, design a path out of vendor lock-in, and manage the entire transition so that the impact on your operation is minimal. You can start anytime, and the sooner the better.


We will assess the situation as a first step
Before we propose any solution, we need to understand exactly what situation you are in. We perform a technical and process audit of your existing software — mapping vendor dependencies, documentation status, technology debt, and risks associated with any migration. Based on the findings, you will receive a specific roadmap with priorities, a timetable and a cost estimate. No general recommendations — just a solution tailored to your system and your business goals.
We take control of your software at every stage
Technical Audit and Dependency Analysis
An effective vendor lock-in solution starts with an accurate diagnosis. We will conduct an in-depth audit of your software — source code, architecture, technology stack, and contractual relationships with existing vendors. We identify critical dependencies, security risks, and areas where outdated technologies hamper your development. The result is a structured analysis, on the basis of which we jointly determine priorities and how to solve them.
Migration and Modernization of the System
Moving from an existing vendor or legacy system to a modern architecture is a complex process that requires experience and precise management. We ensure secure data transfer, gradual or complete replacement of obsolete components, and deployment of open technologies that will not bind you in the future. We manage the entire process with regard to the continuity of your operation — without interruptions and without unnecessary risks.
Setting the conditions for long-term independence
Vendor lock-in occurs where clear ownership rules and transparency are lacking. From the beginning of cooperation, we set the conditions that protect you: source code, access to infrastructure, complete technical documentation — all this always remains in your hands. It's not just a technical solution, it's about setting up such a collaborative model that gives you real control over your own system.


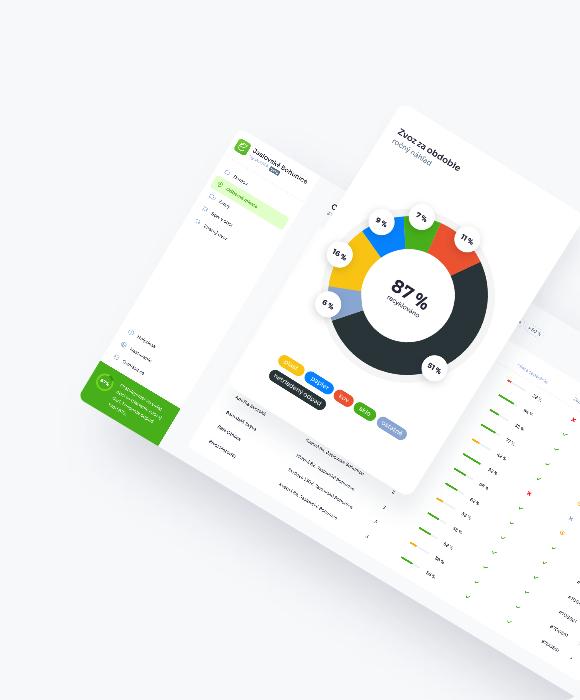
We've saved a lot of coalitions
We successfully completed a number of projects where clients came in with a system tightly tied to the original vendor or at the edge of functionality. Today, they have modern, scalable solutions and full control over their software. It's best if you ask them directly.


Vendor lock-in is in most cases the result of poorly set terms of cooperation at the beginning of the project, not malicious intent. Therefore, we always work transparently: the client owns the source code, has access to all systems and receives documentation on an ongoing basis. Our goal is to add value, not perpetuate addiction.